Each time you visit a new website, your computer will submit a request to the DNS (domain name system) in order to translate the domain name into a numerical IP address.
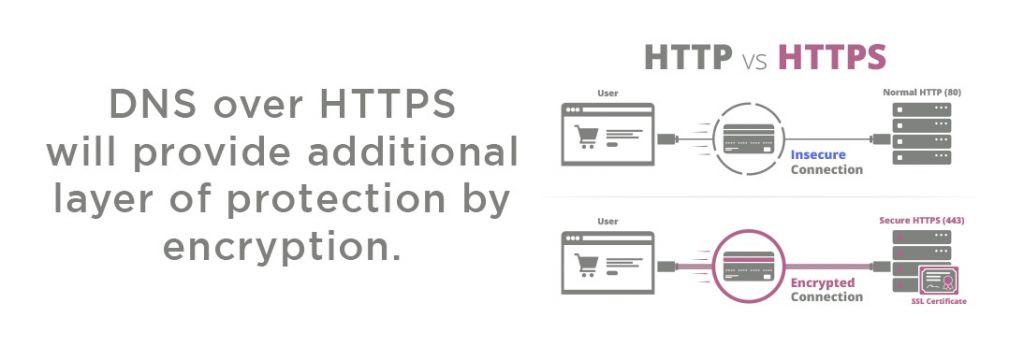
The current DNS system which is in place runs these queries unencrypted which raise privacy and security concerns. Modern internet browsers are trying to address this issue by adding support for sending DNS queries over the encrypted HTTPS protocol (DoH).
Great, unless you are a government or an ISP which wants to spy on its users, or filtering systems used by many companies.
DoH implementation issues ?
The problem with unencrypted DNS is that it is easy for a “man-in-the-middle” to change DNS query answers to route unsuspecting visitors to their phishing, malware or surveillance site.
Major Internet service providers have begun lobbying and in September 2019 a letter was sent by Big Cable and other telecom industry groups warned that Google’s support for DNS over HTTPS would “interfere on a mass scale with critical Internet functions, as well as raise data-competition issues.”
Now, Google says that these concerns have no foundation. Regarding the insinuations from telecom companies, Google said the company has no plans to switch Chrome users to its DNS servers.
While Google didn’t mention it, the company has plenty of ways to monitor users’ browsing patterns with or without access to their DNS queries. What does this all mean?
What DNS over HTTPS mean for ISPs?
It is understandable why telecom companies have issues such as concern that switching to encrypted DNS would prevent ISPs and others from spying on their users, because these companies are accustomed to collecting user browsing data, and in many cases making a profit from selling this data to a third party.
The lack of DNS encryption is convenient for ISPs. For example, queries to malware-associated domains can be a signal that a customer’s computer is infected with malware. In some cases, ISPs also modify customers’ DNS queries in-flight.
Another useful example, an easy way to block children from accessing adult materials is with an ISP-level filter that rewrites DNS queries for banned domains.
In other cases, some public Wi-Fi networks use modified DNS queries as a way to redirect users to a network sign-on page.
Encrypted DNS would make all of these much more complicated or even impossible to do in-flight.
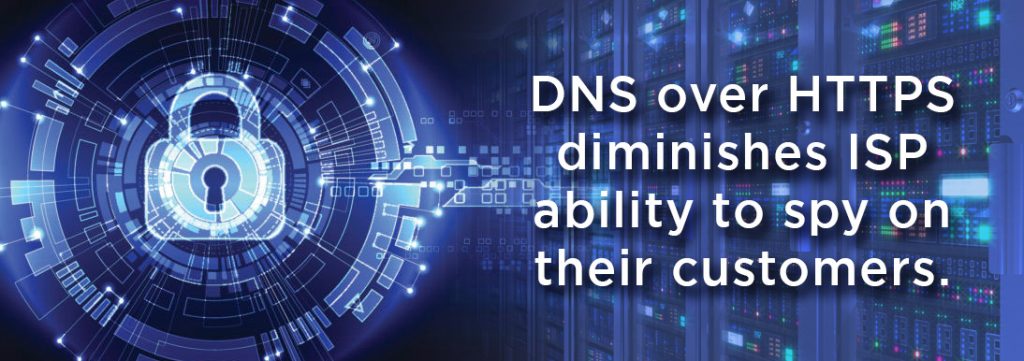
What this means is that DoH would severely limit ISPs’ ability to monitor and/or modify user queries, the ISPs would no longer have an easy way to tell which websites customers were accessing.
Yes, ISPs could still see which IP address their customers have accessed, which will provide them with some information, but multiple domains can share one IP address, and domains can change IP over time, which will limit ISP monitoring of their users.
DNS over HTTPS means users will have a higher level of privacy?
Yes, by users switching to DNS over HTTPS, the ISP will have much less ability to spy on their customers’ browsing ability, which is the main point of this technology. Users should be in charge.
The Mozilla Firefox is a browser that is renown for its user privacy policy and the company is more aggressive than Google with steps taken to avoid making chaos in the process. Firefox will check for parental control software or corporate Intranet features that use specific DNS servers, and if so, the browser will continue using the traditional DNS system.
On the other side, Google has enabled DoH for a small number of whitelisted DNS providers, again to avoid issues, and if needed they too can implement further detection measures similar to Mozilla.
Internet Service Providers spying on their customers can be considered an issue that was never meant to be exploited because users crave privacy. More and more websites are adopting HTTPS because they want to provide their website content securely and privately to their users.
Concerns and conclusions
The encryption of DNS is a natural next step toward a better, more secure Internet. While it will require some painful adjustments by internet providers, that hardly seems like a reason to block the change.
A true concern, which has far more grounds, is that when millions of users switch over to Google’s DNS servers, it is leading to a dangerous concentration of control over DNS.
For the end-user, ordinary people who browse the internet, yes, DNS over HTTPS will make it harder for ISPs to monitor or modify DNS queries, making their browsing experience more secure and private.
Right now, Cloudflare offers DNS resolution over an HTTPS endpoint. If you build a mobile application, browser, operating system, IoT device or router, you can choose for your users to use the DNS over HTTPS endpoint instead of sending DNS queries over plaintext for increased security and privacy of your users.
Encrypted DNS queries must become a reality before a larger number of devices enter Internet-of-things, or we will face an alarming number of DDoS attacks from refrigerators and toasters that are exploited by hackers.